With the hacking of the Democratic National Committee and its influence over the United States presidential election, it’s evident now more than ever that the United States needs a technically literate work force.
Slowly the US education system is integrating more computer science into its curriculum, but very few schools are integrating cyber security curriculum despite it being one of the fastest growing and most understaffed fields today.
Unfortunately, it’s understandable why. There are barely enough cyber security professionals to fill the workforce, much less teach students. In addition, there are a myriad of problems with cyber security education that make it difficult to learn critical cyber security techniques.
In the cyber security world autodidacts are generally the most successful. There are mentors and advisors but the incredible complexity behind computers and computation generally mean that it’s up to the student to actually learn and apply the intricacies of cyber security techniques.
Despite difficulties in education, there can be an almost viral effect amongst students learning cyber security. One student solves a problem and by sharing that technique with others, they effectively teach each other. In addition, light competition can promote self reliance, sportsmanship, and teach good research abilities.
Although most cyber security professionals are self-taught, many got into the field after only a little exposure. At many colleges in the nation, cyber security clubs are created with very few founding members and little faculty backing. If the education system isn’t ready to teach cyber security, maybe we can inspire young students to take it up for themselves.
Computer Science for Cyber Security
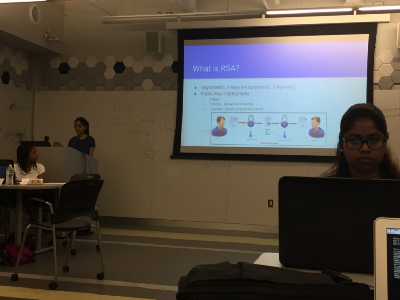
At NYU Tandon, my alma mater, the Computer Science for Cyber Security (CS4CS) summer program provides a free introduction to cyber security for high school girls. The syllabus covers topics like cryptography, web security, and forensics.

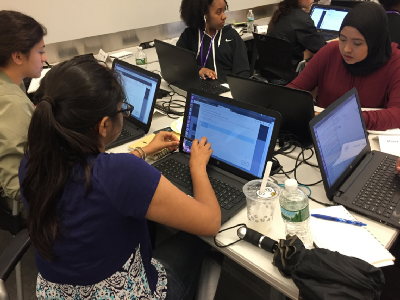
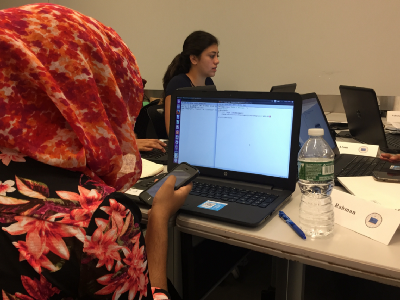
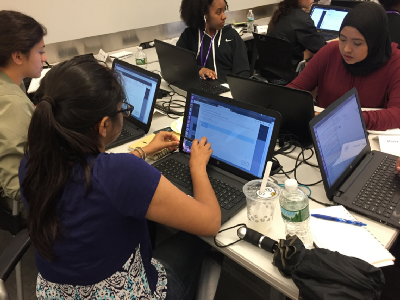
This year CTFd LLC provided free content and a hosted CTFd instance for the program that the girls could hack on throughout the three week program. The students worked on problems ranging from recovering files from a flash drive image to implementing simple cryptography solutions.
One challenge asked the students to implement a textbook RSA algorithm by sending their Python code up to the CTFd server. Their code is fed input and the generated output is checked for correctness. Very much like a programming contest.
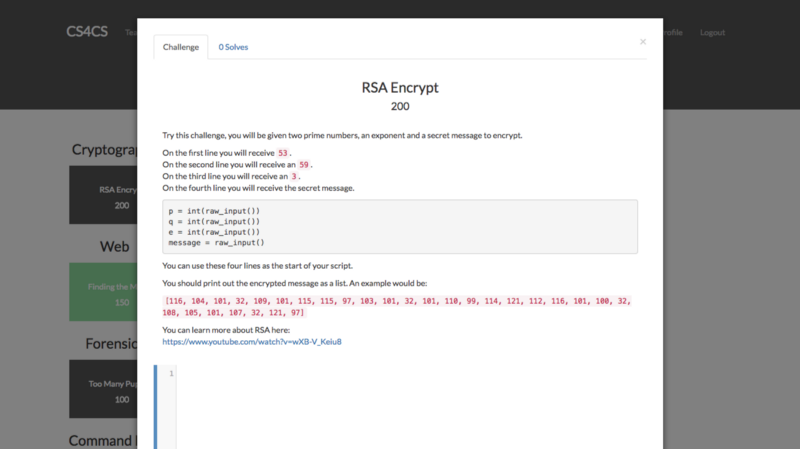
The students had a lot of fun and could interact with the actual material of the lesson instead of just listening to a lecture. The teaching assistants involved could immediately see the steps each student took and help them debug their code. Perhaps best of all for the teachers, they didn’t need to grade any assignments because CTFd checked them already.
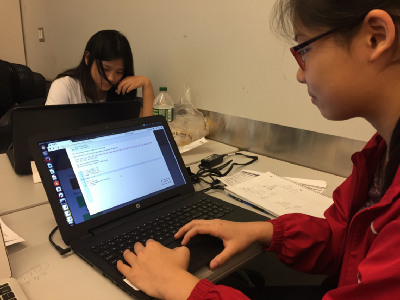
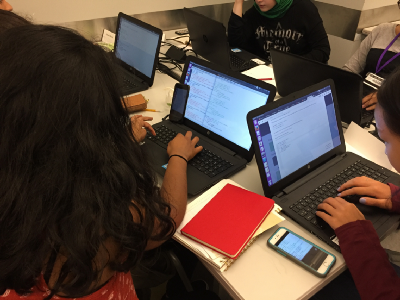
The ACM-esque style of the programming challenges provides a simple way to get started in both competitive programming and Capture The Flags (CTFs). Not to mention, that many of the students have never programmed before. Having an immediate way to run code and check its correctness alleviated the overhead on the teaching staff who would have had to manually setup each student’s laptop.
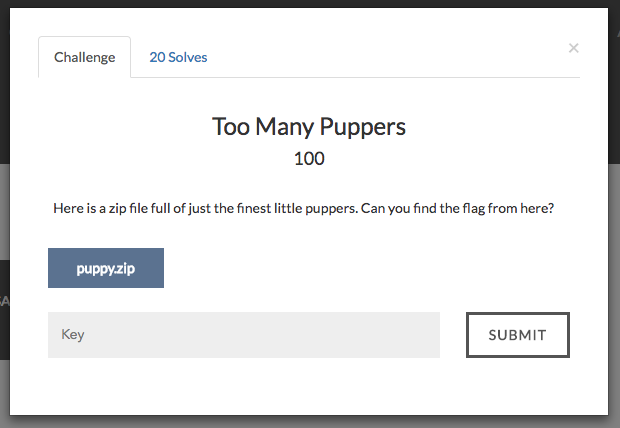
Despite expanding to support programming challenges, CTFd will always support challenges that simply accept a small answer value (or flag as CTF players call them). We asked students to play with their command line and find the secret flag inside a zip file full of puppy photos.
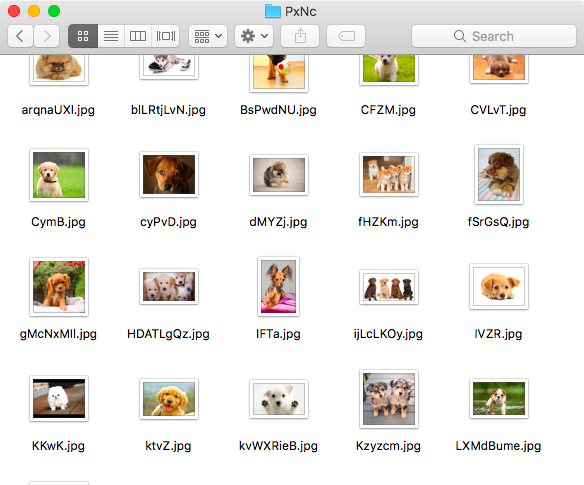
Of course a human would get distracted here, but it’s not a problem for a computer. But in a way, that’s sort of the point. We should always aim to teach with topics that are interesting to students and capture their attention and imaginations.
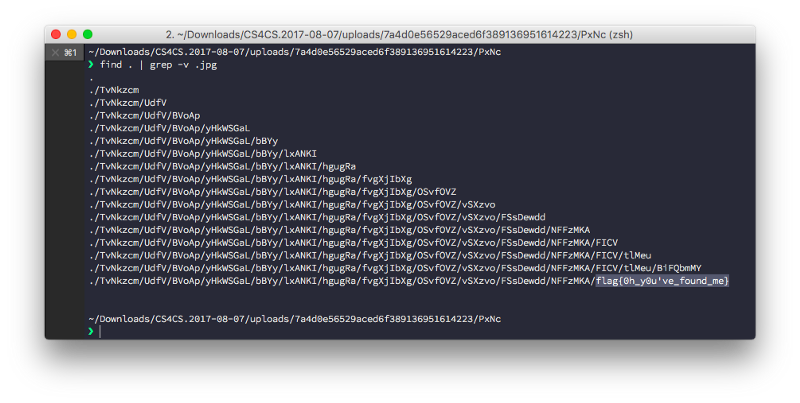
A simple find command later, and 20 students have gotten exposed to their terminals and now know how to search through large piles of files.
HackerFire

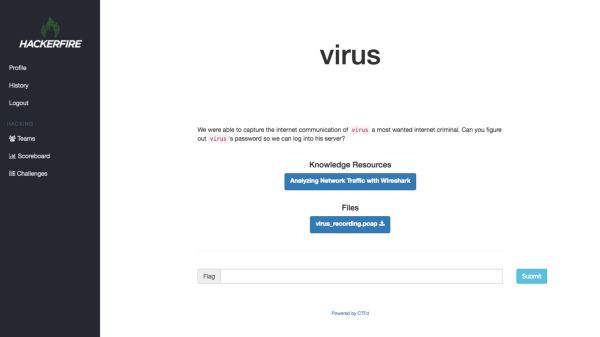
At the end of the program, the students registered onto HackerFire, a public CTFd instance focused on teaching basic cyber security. HackerFire has challenges and knowledge resources that teach topics like:
- Web Penetration Testing — Testing websites for security flaws
- Digital Forensics — Analyzing files and data for forensic evidence
- Reverse Engineering — Taking apart programs to figure out how they work
- Binary Exploitation — Exploiting vulnerabilities in programs
- Network Security — Testing and identifying flaws in a computer network
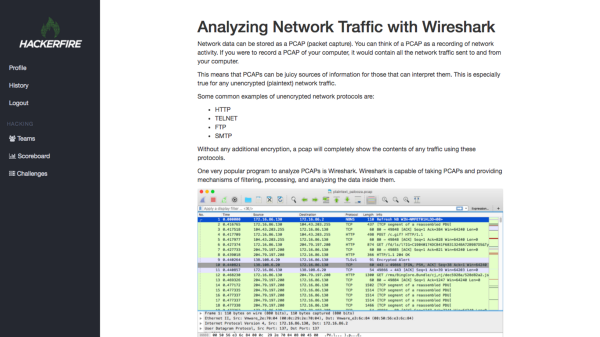
But what differentiates HackerFire from most other CTFs is that HackerFire provides knowledge resources as part of the problem. If a student is struggling, they can refer to the resources for hints about what they should do to solve a problem. For example, if a student has never heard of Wireshark or a PCAP before, they might get stuck on a relatively simple challenge. Instead, HackerFire provides students with
CTFs don’t really fit the standard closed book test model and that’s been very good for CTF players. The closed book test has failed today’s students and as most college students will gladly demonstrate, the bulk of test studying and preparation is done the night before.
As top CTF teams will attest to, there is a good deal of practice involved in being considered “good” at hacking competitions. However, CTFs aren’t about memorization or regurgitating facts on the spot. They’re about knowing the technical foundation behind modern computers and applying them to strange, new problems. HackerFire tries to give students the knowledge they need to get up to speed without needing to find resources elsewhere or guess unnecessarily.
With a little help from the knowledge resources, the students were able to go from no programming experience, to writing real code, to solving a wide variety of security challenges in just a few days!
By providing problems that represent real world situations, the students can have fun while learning something valuable and CTFd can be extended to support many different kinds of challenges.
If you’re interested in using CTFd or HackerFire at your company or educational institution, let us know.
Huge thanks to Phyllis Frankl and Meghan Clark for making CTFd part of their curriculum!